A brief story of sharing educational resources
In the software community, the Open Source movement encourages sharing software freely. Whether it’s “free of charge” (one type of freedom) or “free to use these materials and modify in any way you wish” (a different type of freedom altogether), these people share the work they’ve done and the rights to use their work with the larger community.
In the education community, too, there is a long history of teachers sharing resources with each other. From worksheets to lessons plans, from presentations to assessments, we have all benefitted from the experiences and work of our peers at one time or another.
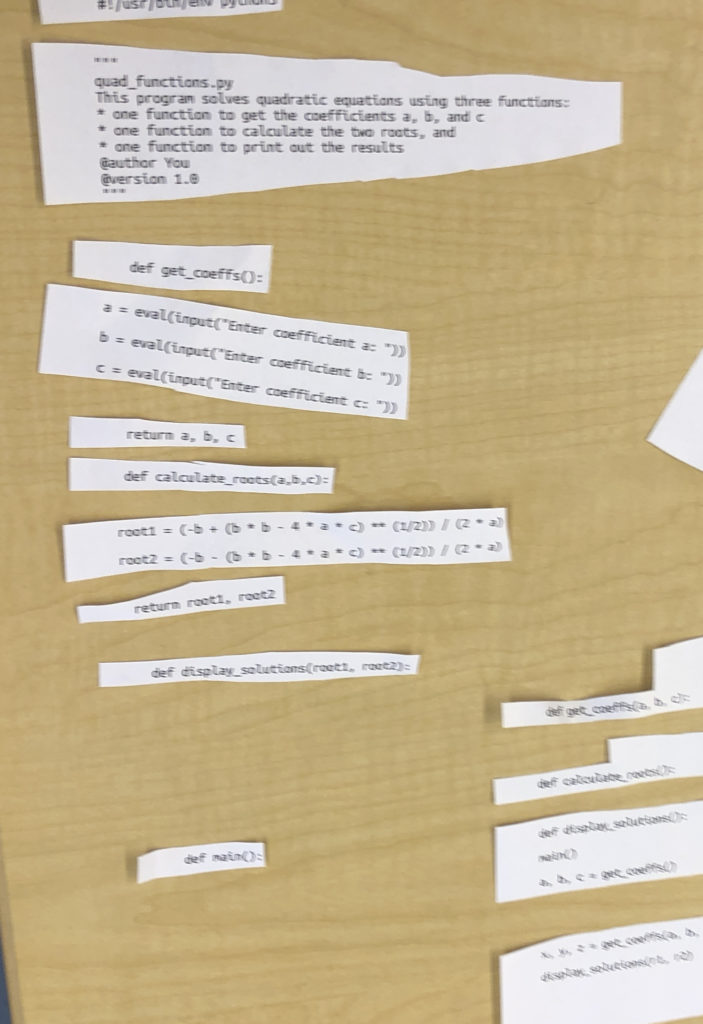
In my own teaching career I have moved from being a borrower of others’ materials to a creator of my own. Computer programming assignments from Cindi Mitchell, physics lesson plans from Dennis Wittwer, Don Hubbard, and Carol Wawrukiewicz, and pedagogical strategies from Aaron Glimme have all informed what I teach and how I teach. A few years into my career I began developing the confidence to share my own growing expertise with others, and learning how to publish my own materials on the World Wide Web was a turning point. Since then, I’ve been happy to share much of what I do professionally on my course websites, even as my own practice continues to evolve.
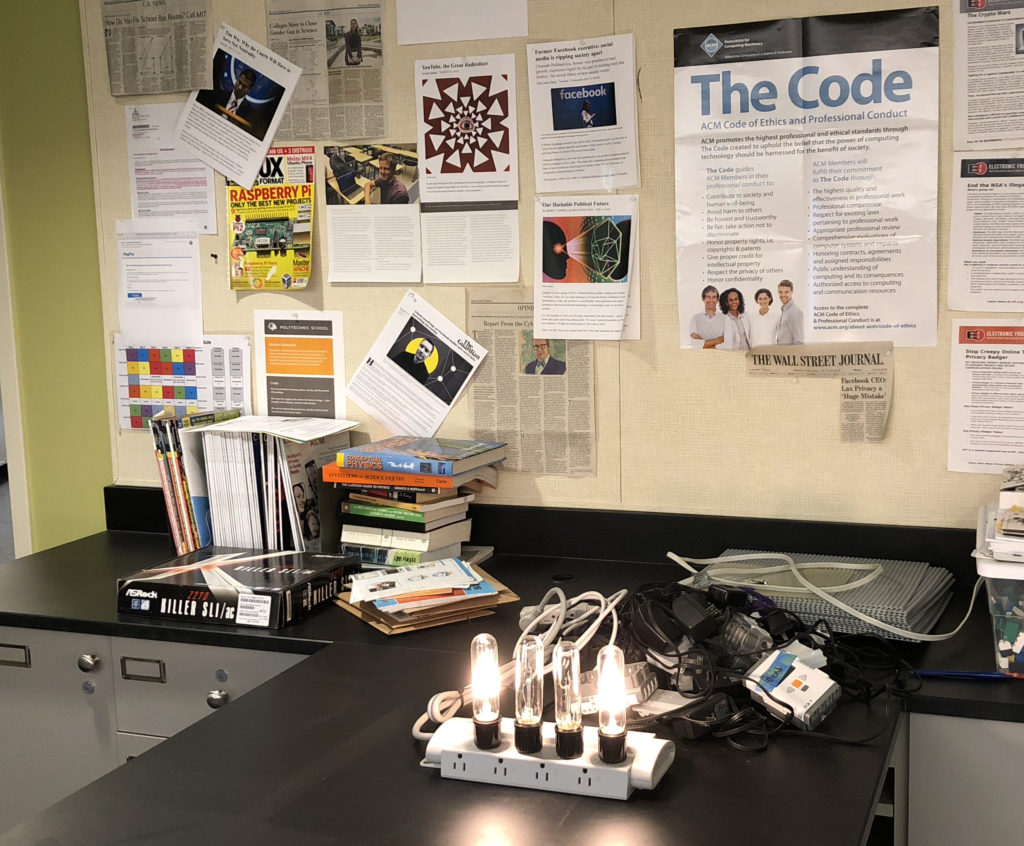
For a number of years now, teachers at Poly have been using the school’s internal website, MyPoly, to help organize and manage resources for their students. Some teachers also maintain public-facing websites where that information is available to others outside our community. (See Greg Feldmeth and Craig Fletcher” for examples.) These websites typically don’t share everything a teacher does—test keys and personal student information wouldn’t be appropriate for posting-—but assignments, practice materials, and even homework solutions might be found.
It’s not unusual for a teacher who shares materials to receive emails like this:
Hello Mr. White!
I’m teaching AP Physics 1 for the first time at Crescent Valley High School, in Corvallis, Oregon.
I came across your website while searching for materials to use for a pre-assessment.
Would it be all right with you if I include some of your questions in the document I give to my students? I’d be happy to return the favor at some point if it’s ever useful.
Thanks in advance and I hope the new year is treating you well.
Take care,
DB Science Department Crescent Valley High School
Occasionally a student will write asking for assistance of one kind or another. I received one such request from a student in Maryland just after the Thanksgiving Holiday in November, 2018.
Hello Mr. White,
My name is Zeke Nohr, a senior at Aberdeen High School. Over the brief Thanksgiving break, our physics teacher resigned very unexpectedly. The school in the process of finding a replacement for him but as of now, me and 5 other seniors who are very skilled and interested in physics have been placed in charge of planning the curriculum for his physics classes. Two of the classes are AP Physics C: Mechanics which we all took last year so we have all the resources we need for that. The other two are AP Physics C: E & M which we are currently enrolled in. We have some resources that our teacher left behind but we are missing practice tests we would like to use as review materials, especially since we plan on having our next test on Monday or Wednesday next week. Our previous physics teacher frequently used the “Multiple-Choice Practice Problems” from your website, learnapphysics.com, that are displayed with all units. I do not see a way to download these as a document to distributed to our class. If you have those documents available for the Electricity and Magnetism Units, we would be extremely grateful if you could provide us with a copy.
Best Wishes,
Zeke Nohr
I replied, with instructions on how the student could access some of those problems, and provided links to some practice tests that I post online for students, and got a quick reply.
Hello Mr. White,
Thank you so much for taking time to respond to my email and providing me and my fellow students with resources we can use for the rest of the year in our physics class. We are extremely grateful for your help during this transition.
Thank you,
Zeke Nohr
When I shared the story with Craig Fletcher, he thought that he might have some materials that the students would benefit from as well. In a separate email, he sent along his own set of links.
We didn’t think much more of it until we each received an email the day before Winter Break:
Dear Mr. White and Mr. Fletcher,
Hello, this is Zeke Nohr from Aberdeen High School. I sent you an email around the end of November asking for practice tests resources for our physics classes that me and two other students were teaching due to the unexpected departure of our physics teacher. Mr. White first sent me some great practice tests which were extremely helpful and we are all very thankful for your generosity. When Mr. Fletcher sent me the email saying the two of you had discussed it and shared the plethora of resources on your website, including lectures, textbook links, practice tests, and homework problems and solutions, we were all surprised and excited by your generosity and willingness to help us through a difficult time. Luckily, a new physics teacher was found very quickly and he started here on Monday. His name is Viktor Polyak and he recently graduated from college and this is his first time teaching. He is very good at explaining the topics and all of us here at the school like him. Since he is a first time teacher, he didn’t have any teaching resources when he came in so we have been using the lectures that the two of you supplied and they have been so informative and helpful to us (the mechanics classes have especially enjoyed “The Island Series” at the beginning of Mr. Fletcher’s lectures) and we intend to keep using them for the rest of the year. Having these resources has made the transition to a new teacher so much easier as he does not have to spend time looking for lectures and homework problems and can focus on helping us learn. We are all extremely grateful to the two of you for sharing your resources with us in a time when we did not have access to any. Your generosity and compassion is heartwarming and has made a huge impact on us here. I told the other students here that I was sending a thank you email today and some of them wanted to sign the email as well to show their gratitude.
Thank you so much,
The email was signed with the names of 42 students, the school’s program director, and the new physics instructor, Victor Polyak.
Teachers at Polytechnic School find lots of ways to become involved in our community of learning. We are involved with consortiums and cohort groups, we attend workshops and conferences, we teach at summer school or Partnership for Success!, and we work with teaching fellows and mentor new teachers. For me, making course materials I’ve developed available online where they can serendipitously benefit students and teachers in an even broader community has been a rewarding part of my professional life.